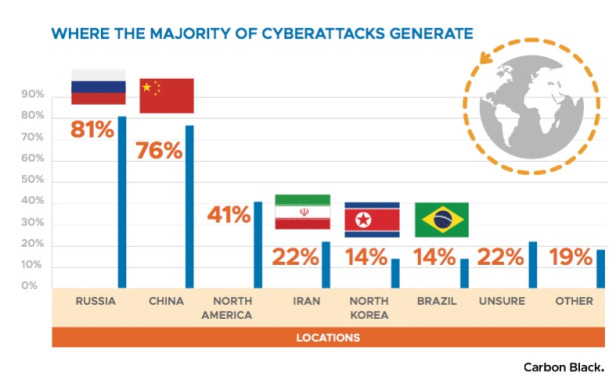
As the world’s attention is focused on cyber crimes such as ransomware and crypto jacking, attackers are busy refining their craft, while nation-states such as Russia, China, Iran, and North Korea are increasingly supporting technologically advanced cyber militias.
 According to Boston-based cyber security specialist Carbon Black’s inaugural Quarterly Incident Response Threat Report (QIRTR), cyber attackers are honing their ability to remain undetected inside the enterprises they’ve breached, and are adjusting their attacks to counter defenders’ response efforts.
According to Boston-based cyber security specialist Carbon Black’s inaugural Quarterly Incident Response Threat Report (QIRTR), cyber attackers are honing their ability to remain undetected inside the enterprises they’ve breached, and are adjusting their attacks to counter defenders’ response efforts.
“If this report reveals anything, it’s that business leaders can no longer get by thinking an attack won’t happen to them,” said Carbon Black, warning that attacks that were once reserved for sophisticated campaigns have become an everyday reality.
“Attackers are using increasingly sophisticated techniques and can easily evade standard defenses, our IR partners noted,” the firm added. “Perhaps most importantly, the consequences of geopolitical conflict can have a tangible impact on global organizations and our connected way of life.”
Other key findings* included:
The vast majority of cyberattacks originate from two nation-states: 81% of IR professionals say the majority of attacks come from Russia; 76% say the majority come from China. And these foreign actors are seeking more than just financial gain or theft — 35% of IR professionals say attackers’ end goal is espionage.
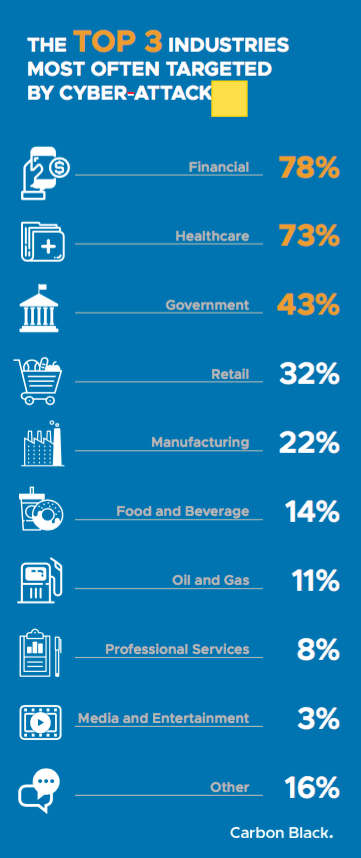
Geopolitical tension is driving an evolution in cyberattacks against all verticals, but 78% of IR professionals say the financial industry is attacked most often; 73% say healthcare organizations and 43% say government.
Nearly 60% of attacks now involve lateral movement, which means attackers aren’t just going after one component of an organization. They’re getting in, moving around and seeking more targets as they go. Of note, 100% of respondents say they’ve seen PowerShell used for attempted lateral movement.
Nearly half (46%) of incident response professionals say they’ve experienced instances of counter-incident response, another concerning sign that attackers have become increasingly sophisticated and are initiating longer-term campaigns — as well as a clear signal that incident response must get stealthier.
More than a third (36%) of today’s attackers now use the victim primarily for island hopping. In these campaigns, attackers first target an organization’s affiliates, often smaller companies with immature security postures. This means that not only is your data at risk, but so is the data at every point in your supply chain, including that of your customers and partners.
Geopolitical tensions playing out in cyber space
Geopolitical tension is a historical constant, but today’s conflicts are increasingly playing out in cyberspace, where subversive acts can be devastating and nearly impossible to prosecute, the report continued. “The result is an evolution in cyberattacks across all verticals, with the financial industry the most frequent target (78% of respondents say as much) followed by healthcare (73%) and government (43%).”
The data revealed that some foreign actors, such as China, are continuing to seek competitive economic advantage, calculating, for instance, that it might be easier to steal IP from an American defense contractor than develop it themselves. “Others have political motives, as seen in Russia’s hack of the Democratic National Committee during the 2016 U.S. election and the recent cyber campaign against the U.S. energy sector,” said Carbon Black. ”As economic pressures and political tensions grow, more and more nation-states are finding it politically and financially advantageous to leverage cyber militias in sophisticated attacks. It is much less expensive (and stealthier) to launch a cyberattack than it is to launch a nuclear weapon.”
The firm said these attackers served as a harbinger for the rise of long-term campaigns highlighted in the report. Seeking to avoid detection, nation-state actors might embed themselves on foreign networks and lay low for years before taking overt action, it said.
“According to one IR professional interviewed for this report, attackers also linger simply because ‘they want to learn — learn the network, where the data is and how they can get it without setting off alarms’,” said Carbon Black.
*The QIRTR report aggregates both qualitative and quantitative input from leading Carbon Black IR partners, who on average participated in one incident response engagement per day over the course of 2017. Data from this report represents insight from active breach investigations where, in most instances, some combination of people, process, and legacy security technology has failed. Of note, several questions from the survey were multi-select. As a result, total figures exceed 100%.
